Transcribed from This is Hell! Radio’s 1 March 2014 episode and printed with permission. Listen to the full interview here:
“This is a collective problem that affects everybody; it’s sort of like our Internet is polluted.”

Chuck Mertz: On the line with us right now: award-winning investigative journalist Julia Angwin. Good morning, Julia.
Julia Angwin: Good morning.
CM: Great to have you on the show. Julia is the author of Dragnet Nation: A Quest for Privacy, Security, and Freedom in a World of Relentless Surveillance. She is a senior reporter at ProPublica; her most recent writing there is last week’s You Know Who Else Collected Metadata? The Stasi. Let’s start there. How much is the United States’ surveillance system on their citizens today like surveillance systems during the Soviet era?
JA: Well, that’s a great question. I was writing this book about privacy, and I’ve been covering this topic for a long time, and people kept raising these comparisons to the Stasi, the East German Secret Police. I thought, is this a hysterical comparison, or is it real? So I went to the Stasi archives in Berlin and I got a few files. And what I found was these files—although the Stasi worked hard to get them—pale in comparison to Facebook profiles or what Google has about you. And that doesn’t mean that Facebook and Google are like the Stasi, but it does mean that there’s a lot more information available to people who want to surveil us.
CM: A company called Silent Circle this week unveiled a cell phone they call the Blackphone. Extremetech.com reported, “the Blackphone is essentially a mid-to-high-end Android Smartphone that comes with a bunch of privacy and security-oriented apps. As far as cryptography goes, the Blackphone’s implementation of Silent Circle’s secure communication apps is pretty darn good. The Blackphone also offers an encrypted file system; the per-app granular permission system is neat.”
However, Phil Zimmerman, one of the Blackphone’s creators, is quoted as saying, “we have a bit of a problem with the press saying that the Blackphone will make you NSA-proof. If someone at Blackphone tells you that it’ll protect you from the NSA, I will fire them.”
Whether it’s global warming or disease or whatever challenge we face, Americans have this belief that somehow, some future technology will save us. How much can we rely on some future undiscovered technology to protect us from being spied on by the government?
JA: Phil Zimmerman is right. You shouldn’t call your technology NSA-proof. Now that we’ve seen what the NSA can do, I think it’s pretty clear that if they want you, they’re going to get you. What I think is a more legitimate thing to worry about is indiscriminate tracking. If you’re not a suspect, do you really need to be swept up into the dragnet? So I try to figure out ways to get out of the dragnet, but trying to escape the NSA’s targeted surveillance is not something most of us have to worry about.
CM: That gets to another point that you bring up in your book: the dragnet presuming guilt. How is it that this hasn’t been challenged in the courts? This is clearly the antithesis of what American law is supposed to be.
JA: Well, here’s the thing: our laws are set up for a time when there wasn’t mass surveillance. We have what a lot of people describe as outdated privacy laws. For instance the Fourth Amendment, which is probably the one that most people think about, is about securing your papers inside of your home.
It’s true that the police still need a warrant to show up at your house and get your papers, but these days our “papers” are now stored in Googledocs. And they don’t need the same standards to get your papers there. A lot of tech companies have been advocating for these laws to be updated, but currently they’re not. So there’s kind of a free-for-all; there’s a lot of information that law enforcement can get, that they didn’t used to be able to get.
CM: Personally I’m a bit concerned, as far as my own security and surveillance goes, because I’ve interviewed people on this show like Sami Al-Arian, who on February 20th had his eleventh anniversary of being imprisoned. We’ve also had former Gitmo detainee Moazzam Begg, who was just arrested in Britain. How much did this ‘chilling effect’ on journalism affect you in the writing and the research of Dragnet Nation?
JA: In today’s world it’s very hard for journalists to promise their sources confidentiality. Edward Snowden, for instance: it seems as though he outed himself because he knew they would find him. And so he wanted to take control of that situation. And we’ve seen the government going after the phone records of journalists, and there’s one New York Times reporter who’s fighting all the way to the Supreme Court to protect the confidentiality of his sources.
So this was actually a big motivation for me, writing this book as a journalist. Could I protect the confidentiality of my sources? And there are some techniques that can be used, but most people don’t want to use them. It’s very cumbersome to sit down with somebody and say, “okay, I know you want to give me secret stuff. First, I’m going to install a bunch of software on your computer, then you’re going to have use special protocols to reach me…” It’s a very difficult situation for journalists these days.
CM: You write, “any of us can be watched at almost any time, whether it is by a Google Streetview car taking a picture of our house, or an advertiser following us as we browse the web, or the National Security Agency logging our phone calls.”
And by the way, I’ve got to mention this: when you are using Google Streetview and you’re, let’s say, going down the streets of New York, it doesn’t seem like anybody really cares. Or Los Angeles or San Francisco or Seattle. It just seems like people are like, oh, there goes a car with a camera on it. A lot of people aren’t even looking at it. Some day, you should go through the streets of Detroit on Google Streeview. Everybody is staring at the camera. It looks like everybody is shocked. It’s the most bizarre thing; you should check it out sometime.
But there’s this rationale that we shouldn’t be so upset about the NSA or marketers spying on us, because we voluntarily give up so much personal information on social media. We give personal information to retailers when we make purchases. Is it hypocritical, or at least inconsistent, to both give up information on Facebook, even allowing it to tell people where you are at all times, and at the same time be critical of the government or retailers or marketers spying on us?
JA: That’s a complicated question. In general, we have gotten used to a world where we don’t think we have to pay for anything. We think that our news should be free and our shirts should be free, and our dictionaries…all sorts of things we used to pay for—email: we used to pay for postage on letters—we want for free. And then we get annoyed when they make us pay with our data.
I do think that we bear some responsibility for our choices. Which is why we need to make more conscious choices.
The problem is that there aren’t that many alternatives. I was able to find a search engine to use that isn’t Google, that is privacy-protecting. That’s great, but I haven’t been very successful in finding an email service that’s as good as Gmail but that’s privacy-protecting. And I’m perfectly willing to pay for it; email is so important to me that it would be a legitimate expense.
But there isn’t a market for that. So we don’t actually have enough choices. The problem is, there’s a nascent market for privacy-protection tools, but they’re too expensive or too hard to find. We need that market to grow.
At the same time, it’s also worth pointing out that when you make a transaction with a company—for instance you go to Bloomingdale’s to buy a sweater, or you go to Amazon to buy a book—you don’t necessarily mind them knowing about you. I’d be happy to have them bring me similar sweaters or similar books in the future.
What I think really bothers people is the invisible third parties who are watching those transactions. That is where the social contract between yourself and the business that you’re dealing with breaks down. Because it’s weird. You wouldn’t normally have that in offline life.
“The only thing that companies get in trouble for is if they say that they will protect your data, and then they don’t. So they just say, ‘we won’t protect it.’”
CM: You write, “dragnets that scoop up information indiscriminately about everyone in their path used to be rare. Police had to set up roadblocks, or retailers had to install and monitor video cameras. But technology has enabled a new era of super-charged dragnets that can gather vast amounts of personal data with little human effort.” So are dragnets successful? I want to know this from two different points of view: are they successful when it comes to security, law enforcement and protecting us from terrorism? And are dragnets successful when it comes to homing in on your preferences as a customer?
JA: Okay, well I’ll take them one at a time. Let’s start with the government. The government dragnets have been described to us, post-Snowden, as counterterrorism. So the way to judge those dragnets, at least the NSA, is on the metric of terrorism. And on that metric, so far the evidence shows that they’re not that successful. There have been several terrorist incidents, most of them luckily unsuccessful—the Underwear Bomber, the Shoe Bomber—but also successful, the Boston Bombing. There was information in their dragnets about these people—who were suspects—and yet they didn’t catch them.
Maybe they have too much information; they’re downing in data. There are slides from the NSA that indicate that the analysts were overwhelmed by the information they were getting. Now, the NSA has said they did thwart these 54 plots, but people who have dissected those plots have found that in fact there’s not one that they could really point to where this information was definitively “how we caught them.” So I think the evidence is just not in. Maybe the NSA can’t share with us the super-secret evidence it has about how well these things really work. But since they work for us—we are their employers—I think we deserve better evidence.
On the commercial side: I have to say, my experience—and that of people I talk to—is that ads which are supposedly “targeted” are often completely wacky. Most of the time the thing that targets me is something I already bought. So I think that it is also only marginally effective.
On the other hand, it’s “just an ad,” right? But I do write about how there are some inadvertent things that can happen with those ads. One story I tell in the book is about a woman who didn’t want to be out to her colleagues at work, even though she was perfectly proud of her sexual orientation. But she was using her computer at work and all these ads for gay cruises showed up on her screen, and one of her coworkers said, “oh, why do you have all those ads?” She’d been revealed to her colleagues. The ads can reveal things you might not want people to know.
CM: You have a whole bunch of different cases of how surveillance has affected people, personally. And it isn’t necessarily government surveillance. That’s a fascinating part about your book, this “indiscreet surveillance.”
You write about the case of Sharon Gill and Bilal Ahmed, who met on private online social network PatientLikeMe.com, which, as you describe, is a password-protected online forum for patients struggling with mental health issues. “Sharon was trying to wean herself from antidepressant medications; Bilal had just lost his mother and was suffering from anxiety and depression. Sharon turned to Bilal because she felt she couldn’t confide in her closest relatives and neighbors. Sharon told me, ‘I live in a small town. I don’t want to be judged on this mental illness.’ But in 2010, Sharon and Bilal were horrified to discover they were being watched on their private social network.”
In the disclaimer, PatientLikeMe told people that they would be selling their information to outsiders, so they ‘shouldn’t have been shocked’ about this. Let’s start with that. Is one of the things we need disclaimer reform? Because we all just click ‘Agree,’ and you have no idea if you just sold your soul to the devil.
JA: If you try to read every one of those agreements for every website that you visited, somebody has calculated that it would actually take you 180 hours, based on a normal person’s web browsing. For a year’s worth. That is just not a reasonable burden. Some lawyers have wondered if these could even be considered “unconscionable contracts.” As in, did you really enter into this contract? Is it really fair to treat this as a legally binding agreement?
But there is no baseline standard. We don’t have a law in this country that says you can’t ask people to agree to ridiculous things in those terms. The way that you can’t sell a lemon car; you’re on the hook for that if you’re the seller. But we don’t have a similar law for websites, so they just write in there, “yeah, we’re going to do whatever we want with your data,” and they feel free and clear.
Right now, most enforcement about data abuses is done by the Federal Trade Commission, and they mostly enforce on deception. You have to have deceived the consumer. The only thing that companies get in trouble for is if they say that they will protect your data, and then they don’t. So they just say, “we won’t protect it.”
CM: That’s insane. So why can’t we just say if this is what’s going on at PatientLikeMe, well, the market will fix that, and everybody will leave PatientLikeMe? Why can’t we just “let the market decide?”
JA: Like I said, I switched off of Google’s search engine. There are a few things where we have choices. And I think we should try to exercise those more, because they are important. But at the same time, there’s no incentive for these companies to switch away from the personal data market because that’s what advertisers have come to demand. That’s what they believe they should get out of the Internet: the ability to track you and identify you down to this incredibly granular detail. That’s the whole business model.
So we are probably going to have to start paying for things that we think we want to keep private. But there has to be a baseline standard; we don’t have any lower bounds for how badly people can treat your data. It’s really a Wild West that rewards the most aggressive companies.
“People who have had experiences with surveillance often become much more cautious about what they say. But that’s why my family came over from the old world many generations ago, exactly that. They didn’t want to be in a repressive environment where they felt afraid all the time.”
CM: That leads me to my next question. You write, “it was entirely legal for PatientsLikeMe to disclose to its members in its fine print that it would sweep up all their information and sell it. This is the tragic law of ‘privacy in the digital age.’ Privacy is often defined as freedom from unauthorized intrusion. But many of the things that feel like privacy violations are ‘authorized’ in some fine print somewhere.”
Could law curtail surveillance? Can law trump NSA technology?
JA: The law would certainly be a great start. The NSA says that it is operating within the law. That’s a debatable point, because the President’s advisory committee itself said that the phone dragnet was unconstitutional, but it hasn’t been tested by the courts. But putting that aside, it is worth remembering that we’re the only Western nation without a baseline privacy law that gives people very basic access to the data collected about them; they can see it, correct it, sometimes delete it.
That is something that most of the European nations have and we don’t, and it is actually kind of a tax on the data collectors. They have to think a little bit before they collect the data, about how they are going to provide access. It raises the cost to them a little bit, which hopefully curtails a bit of the surveillance, and also gives people the right to see it.
CM: Glenn Greenwald has argued that the NSA spying he has revealed, courtesy of Edward Snowden, isn’t really about security or terrorism. In November, he told CNN’s Christiane Amanpour that the surveillance is “clearly about political power and economic espionage.”
JA: Information is power. A place like the NSA that has massive amounts of information about us has a lot of power. Whether we have the right checks and balances to restrain that power is the question we have to ask of all governments. They could use it for economic espionage; they could use it to quell political dissent (they say the aren’t). We need to figure out whether there is enough oversight to make sure that won’t happen.
Right now members of congress who wrote the law authorizing the NSA’s activities, the Patriot Act, are saying “actually that’s not what we meant you guys to do with this.” So I think we can say that the oversight probably hasn’t been enough.
CM: What do you think will happen first—will we be turned off by technology, or will we be able to turn off its spying capabilities? Because you write, “new tracking technologies are just around the corner. Companies are building facial recognition technology into phones and cameras. Technology to monitor your location is being embedded into vehicles. Wireless ‘smart-meters’ that gauge the power usage of your home are being developed. And Google has developed Glass, tiny cameras embedded in eyeglasses that allow people to take photos and videos without lifting a finger.” So what will happen first, are we going to turned off by these kinds of technologies that we know the government is now using to spy on us? Or will we have the ability to turn off those spying capabilities?
JA: I’ll tell you what I’m afraid will happen, and then I’ll tell you what I hope will happen.
What I’m afraid will happen is that as we become more and more aware of how much we’re being monitored by the government, by commercial entities, by our neighbors—who can also afford surveillance technology these days—we are going to be afraid to say things. People who have had experiences with surveillance often become much more cautious about what they say.
I am basically unwilling to write anything of any importance in email anymore, because once I realize where it’s going and how long it’ll be stored, I just think, you know what, I’ll just wait and we’ll meet in person in a cafe and talk in a dark corner. And I don’t know if that’s the world we want. That’s why my family came over from the old world many generations ago, exactly that. They didn’t want to be in a repressive environment where they felt afraid all the time. I’m concerned about that scenario.
“It might be worth pointing out that it is unrealistic to think that we can catch every crime before it happens. Right? There was a movie about that.”
However, there’s a book review of my book which says “Julia Angwin is irrationally optimistic,” and I think that’s probably true. I really hope that we can address this situation, and I think that technology can help solve it, too. I am trying to use encryption for a lot more of my emails and to store my files, and I think that advances in technology could help us protect our data.
It also serves as a sort of political vote. The more people use encryption, the more metrics there are about how much people care about this technology, and that affects the political debate.
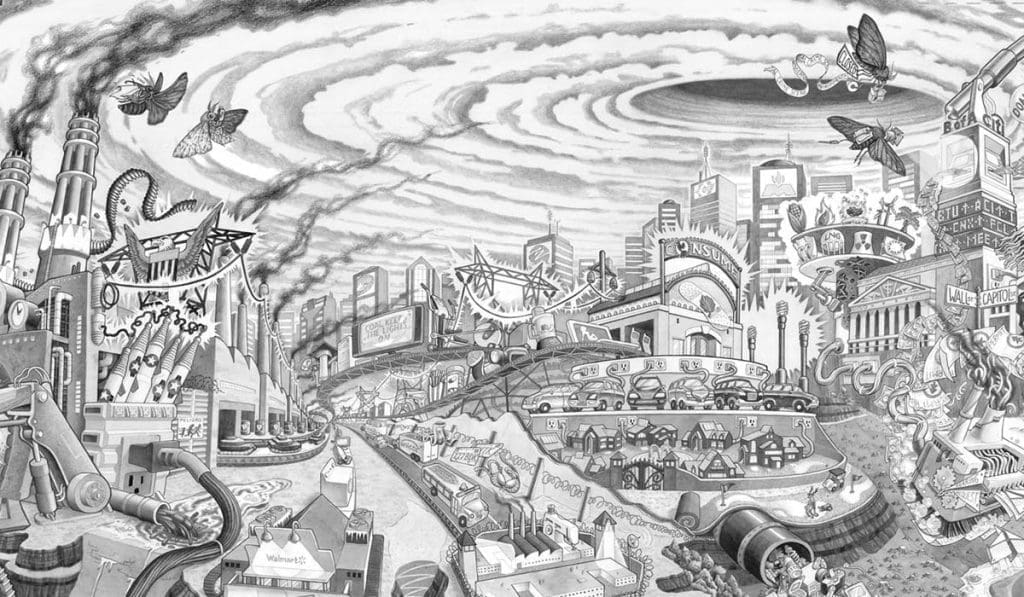
I also think that these problems are often solved over the long run. There was a time in our country where the Cuyahoga river caught fire every couple years because it was so polluted. Eventually we decided we don’t want to live like that, and we passed laws and we changed our behavior. And it took a whole array of things; we had to do our recycling at home, but we also had to pass the Clean Air Act and the Clean Water Act. This is a collective problem that affects everybody; it’s sort of like our Internet is polluted. So I think it’ll take a lot of time and a whole bunch of actions, including collective action, to solve it.
CM: You write, “we are living in a Dragnet Nation, a world of indiscriminate tracking where institutions are stockpiling data about individuals at an unprecedented pace. The rise of indiscriminate tracking is powered by the same forces that have brought us the technologies we love so much: powerful computing on our desktops, laptops, tablets and smartphones.”
There are those conspiracy theorists out there who believe this was the plan all along. The Internet was created by the Defense Department! All along it’s been meant to be a surveillance tool, and has been since its inception. We’re just finding out now! What would you say to a conspiracy theorist who asked you that?
JA: I would say no, that’s not true. In fact, the Internet is so great because it was built by the Defense Department to be decentralized. The whole point of it was to have a system of communications that wouldn’t break down in wartime if one part of it went down.
Centralized systems, if you bring down one central point, then everything goes down. The beauty of the Internet is your packets jump all over the world—parts of your email might go one way and parts might go another way. Interestingly, no one has ever really brought the whole Internet down. Some countries have switched off the Internet in their country during a revolution, we’ve seen that once or twice, but only for a day or two. So it’s an incredibly robust system.
However the problem is that decentralization also means there’s many, many surveillance points. You don’t just set up one in the middle. There are so many spots where you can peek in. So governments are peeking in. And so are other people. We have to figure out how to protect those endpoints.
CM: One last question for you Julia, and it’s the same thing we do with all of our guests, we ask them the Question from Hell: the question we hate to ask, you might hate to answer, or our audience will hate the response. We’re being told we either have to give up our privacy or be attacked by terrorists. You also bring in the whole idea of marketers watching us as well. So this leads to a rather misleading question with a false dichotomy. Are you ready?
What would you rather do: give up your privacy or be attacked by terrorists? What would you rather do: get good deals from stores that you like to shop at, or get bad prices?
JA: Those are two separate questions, okay. So for sure I’m willing to give up my good deals at the stores, because I have to tell you, it never really works out to be a good deal. It really never does. You sign up for that credit card to get the discount, and then they charge you some insane interest rate. Those I’m perfectly willing to give up.
I don’t want to give up security. But as I said before, I have seen no evidence that this mass dragnet surveillance does anything to protect us from terrorism. If it did, then maybe I’d be willing to do it. But currently the evidence suggests the opposite. The people who are looking at this data are drowning in data, can’t see the forest for the trees, and are not catching people who are in the databases before they act.
It also might be worth pointing out that it is unrealistic to think that we can catch every crime before it happens. Right? There was a movie about that.
Are we holding these people to the wrong standard? I think we’re all in favor of catching criminals after they act, and hopefully we can try to prevent people from becoming criminals, but the world of pre-crime is not a world I want to enter into.
CM: Julia, it has been a pleasure speaking with you this morning. Thank you for being on our show this morning, I really appreciate it.
JA: This was great, thank you so much.